Home > News & Blog > Building a Hardware Root of Trust
Building a Hardware Root of Trust
Part III of the Secure Provisioning: Essential Security Measures for the IOT series

Incase you missed Part I - What is Secure Provisioning?, or Part II - Encryption: Symmetric and Asymmetric Keys, you can catch up here.
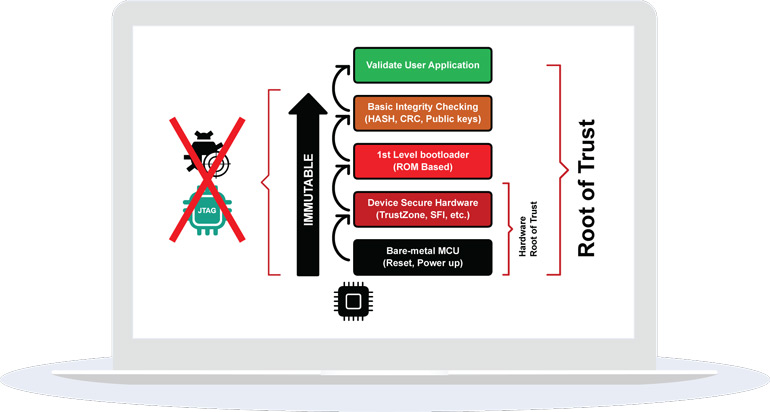
A hardware root of trust (RoT) is the basis for ensuring security in an embedded system. It is based on the idea that an intelligent system has an immutable (non-interruptible) and repeatable sequence that must be executed during initialization. It can include additional functions that are not limited to those listed below:
- A Trusted Execution Environment (TEE)
- Some cryptographic functions (AES, True Random Number Generator)
- Secure services available to the main application (signing, verification)
The TEE can be expanded on and can include hardware security measures specific to the vendor microcontroller. An example of this is Renesas's Trusted Security IP (TSIP). With these technologies, cryptographic keys, along with other secret information, can be stored securly within the microcontroller and form an important part of the RoT.
When an intelligent system includes a RoT it can be guaranteed that the microcontroller that usually forms the heart of the system, will follow a set sequence of instructions on being released from reset.
This is where secure provisioning comes to the fore. There are many purveyors of software security solutions that can purport to being able to secure your software, but they often depend on a RoT. This is very typical in the mobile telecoms arena where the RoT is usually based on a hardware TEE. Secure provisioning ensures that, for an embedded microcontroller-based system, the RoT is programmed (provisioned) into the bare-metal microcontroller in a secure manner. This ensures the integrity of security functions used in the upper layers of the system that are dependent on a hardware RoT.
Coming up in Part IV: Digital Certificates & Signatures.
In the meantime, if you have any questions or require secure provisioning services get in touch, we have local engineering and sales teams ready to help. You can find a full list of our locations here.Alternatively if you have any questions or would like us to focus on additional topics around IOT security and provisioning in future blogs, don’t hesitate to let us know: programming@epsglobal.com.
Continue Reading: Part IV - Identity: Digital Certificates & Signatures








