
ABOUT INTRINSIC ID
Intrinsic ID is the world’s leading provider of hardware-based security IP. Our Physical Unclonable Function (PUF) based digital authentication technology is used as a hardware Root of Trust to protect ICs from cloning, counterfeiting, and prevent theft of IP and overbuilding in the IC supply chain. Our PUF technology is deployed in IoT devices, datacenter chips and connectivity/communications devices, and has been deployed in defense electronics for a decade without breach or failure.
SRAM PUF
Intrinsic ID delivers strong, device-unique data security and authentication solutions for the connected world. These authentication solutions are based on Intrinsic ID’s patented SRAM Physical Unclonable Function or SRAM PUF technology.
Using this technology, security keys and unique identifiers can be extracted from the innate characteristics of each semiconductor. Similar to biometrics measures, these identifiers cannot be cloned, guessed, stolen or shared. Keys are generated only when required and don’t remain stored on the system, hence providing the highest level of protection.
Intrinsic ID's SRAM PUF-based security solutions are very suitable for applications such as secure key generation and storage, device authentication, flexible key provisioning and chip asset management. They can be used to secure payments, to protect highly sensitive data, for anti-counterfeiting and anti-cloning, to prevent identity theft, piracy of media content and software apps, software reverse engineering, and more.
Security Based on SRAM PUF
At power-up, SRAM bits settle in the one or zero state in a non-deterministic way that not even the manufacturer can predict or duplicate. That’s what makes it a physical unclonable function, or PUF, which can be used as a unique "silicon fingerprint".
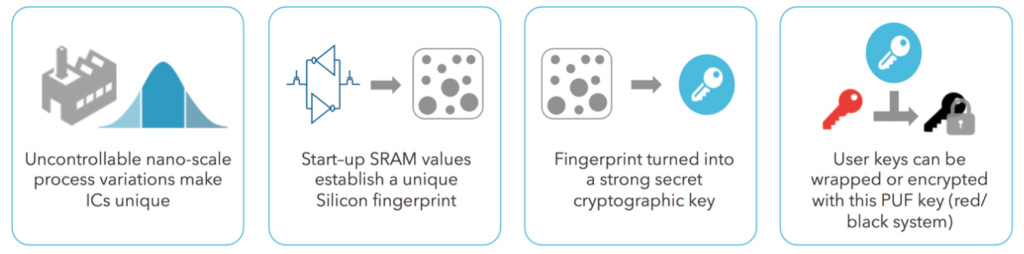
An SRAM PUF response is a noisy fingerprint, and turning it into a high-quality and secure key vault requires further processing. This is done with the QuiddiKey hardware IP. QuiddiKey reliably reconstructs the same cryptographic key under all environmental circumstances. Upon first use, called the enrollment, it generates an activation code (AC) which, in combination with the SRAM startup behavior, is used to reconstruct on demand, in real time, an intrinsic PUF key. This PUF key is never stored in flash or OTP. When it is needed later it can be reconstructed.
The intrinsic PUF key can be used as a root key for key derivation and key wrapping. A key protected by QuiddiKey is integrity protected and can be retrieved only on the same device while it will be meaningless on other devices.

